The Perimeter of
Breach Prevention.
Every employee with a browser is a potential data leak. The AIEGES Shield classifier inspects prompts, files, and browser submissions before they reach ChatGPT, Gemini, or any third-party AI service. Catch leaks before they become incidents.

Your People Are the #1 Attack Surface.
Perimeter firewalls protect servers. Shield protects you from everyday AI usage. Every time someone pastes client records into ChatGPT or uploads source code to an AI assistant, your organization faces HIPAA penalties up to $2.1M per violation category, compliance litigation averaging $400/hr in billable defense, and breach settlements that routinely exceed $1M. Shield classifies sensitive data at the browser edge — before it ever leaves your network.
Billing Manager pricing
Checkout plans synced to the live AIEGES catalog.
The hub now exposes the same four self-serve Shield plans currently available in Billing Manager: 1, 10, 25, and 50 seat bands with monthly and yearly checkout paths.
Individual
Secure your local AI usage with zero-trust browser interception, local redaction, and downloadable audit evidence.
Single machine protection
individual access
- Browser interception
- Local redaction path
- Prompt + file screening
- Downloadable audit trail
Small Team
Standardize browser and gateway guardrails with centralized policy management for the first team rollout.
Standardized for 10 users
10 seat activation
- Shared policy controls
- Team rollout baseline
- Gateway + extension coverage
- Centralized enforcement
Business
Add compliance-ready audit trails, richer team analytics, and broader rollout coverage for regulated operations.
$11.99/seat billed monthly
25 seat activation
- Compliance-ready reporting
- Advanced audit visibility
- Expanded team governance
- Higher-volume coverage
Organization
Roll out full-fleet protection with the largest self-serve checkout tier currently exposed in Billing Manager.
$9.99/seat billed monthly
50 seat activation
- Largest self-serve tier
- Fleet-wide rollout support
- Operational download access
- Org-scale guardrails
Guided rollout
Need procurement support, a rollout beyond the current 50-seat self-serve tier, or a regulated deployment review? Use the demo lane instead of forcing the wrong checkout.
Request guided rolloutHow Shield Works
From browser interception to policy enforcement — see the AIEGES classification engine in action.

AIEGES Shield Extension
Browser-side sensor that intercepts clipboard data, form inputs, and file uploads in real time before reaching any AI service.
Classifier Pipeline
Four-stage classification cascade from browser edge to policy enforcement with three resolution paths.
WASM PII Scanner
Client-side WebAssembly scanner that detects PII patterns in under 2ms. Zero data leaves the browser — no network calls, no server overhead.
Sovereign AI goes further
Runtime is half the story. Security is the other half.
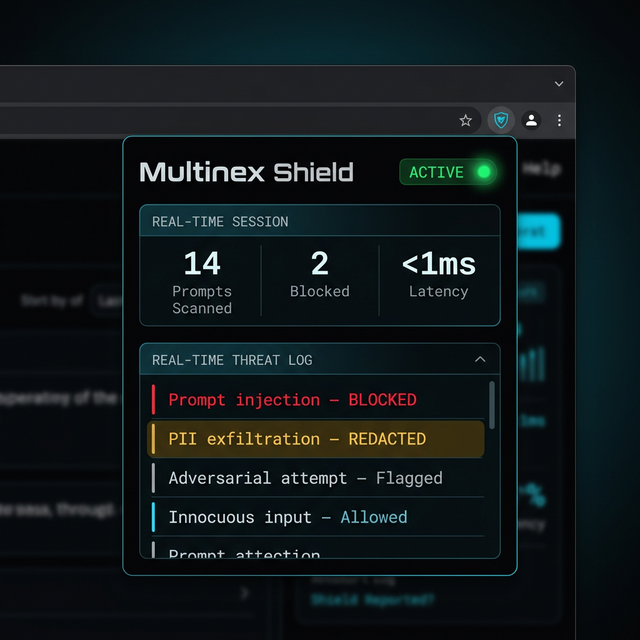
Multinexus puts your AI team on your hardware. But what about the calls those agents make? What about the prompts they receive? That's where Multinex Shield comes in.
Act II — Multinex Shield
Every AI Tool Call. Inspected.
Your AI agents call external tools — APIs, databases, code runners. The gateway doesn't block your workflow. Aho-Corasick pattern matching runs inline at <2ms. Everything else is inspected after it passes through — a breadcrumb-logging agent traces every call, and when a trail is marked bad, it blocks that pattern from coming back.
API CallINSPECTEDDB QueryLOGGEDCode ExecPOLICY-CHECKEDFile WriteBLOCKEDLayer 1 — Inline
Aho-Corasick engine · 147+ threat patterns · <2ms per request
Layer 2 — Async Inference
Llama inference model · Breadcrumb trail analysis · Blocks bad actors retroactively
No unauthorized data exfiltration
No unreviewed tool calls
Full audit trail
HIPAA Compliance
Prevent HIPAA Violations Before They Happen
Multinex Shield acts as an enterprise security layer to automatically solve the most common causes of HIPAA violations—from unauthorized snooping to third-party data leakage.
Curiosity Violations
Snooping & Gossip
Role-Based Access Control (RBAC) and strict audit logging prevent unauthorized employees from accessing PHI out of curiosity.
Social Media Blunders
Background Slip-ups
Real-time output redaction masks PHI on screens, preventing accidental exposure in background selfies or online venting.
Tech & Security Failures
Unencrypted Devices & Phishing
Zero-cloud architecture and forced encryption ensure patient data is never left vulnerable on unencrypted drives or exposed to phishing.
Third-Party Leakage
Tracking Pixels & APIs
The Shield Gateway intercepts and strips PHI before it reaches tracking pixels or unauthorized Business Associates without a BAA.
Browser Extension · Developer Preview
Wallet Signing Interceptor
The Multinex Shield browser extension hooks window.ethereum.request before any dapp code runs — intercepting every signing call, scanning message text through the full detection pipeline, and blocking or flagging risky transactions in real time.
:9999Full 365+ pattern pipeline via the Rust binary sidecar. Start with `aieges sidecar`.
:8080Reuses the running gateway proxy. Extension discovers /aieges/status automatically.
inline18 regex patterns mirroring Shield classifiers C-01..C-06. No binary required.
Signing Risk Matrix
| RPC Method | Risk | Default Action | Detection Logic |
|---|---|---|---|
eth_sign | HIGH | BLOCK | Arbitrary byte signing — always dangerous. Blocked unconditionally. |
personal_sign | MEDIUM | FLAG | Message decoded and scanned for phishing patterns before signing. |
eth_signTypedData_v4 | MEDIUM | FLAG | EIP-712 parsed for MAX_UINT256 approvals, Permit2, Order types, expired deadlines. |
eth_sendTransaction | MEDIUM | FLAG | Value threshold (>0.05 ETH) + selector fingerprinting (approve, transferFrom, setApprovalForAll). |
Everything else | LOW | PASS | Non-signing methods pass through unmodified. |
Hook timing: Injected at document_start via web_accessible_resources, before any dapp JS executes. Late-injection wallets caught via Object.defineProperty.
Fail-open: 15s timeout per signing request. If the extension is slow or unavailable, the original wallet call proceeds unmodified — never bricks a dapp.
EIP-1193 compliance: BLOCK verdicts throw { code: 4001 } so dapps handle it as “user rejected” — no unexpected crashes.
Binary escalation: When the Multinex Shield sidecar is running, eth_signTypedData_v4 message strings are passed through the full Aho-Corasick + PII + entropy pipeline for deep analysis.
One Security Story for Every Regulated Team
Every vertical has a different breach shape. Shield gives each one the same structure: define the risk, intercept the leak, and prove what happened.
Healthcare
HIPAA Compliance
A nurse accesses a celebrity's patient record out of curiosity. Even without stealing anything, it's still a HIPAA violation waiting to happen—regulatory exposure that scales with each incident.
Shield logs every access and flags unusual behavior before it becomes an audit finding. Role-based alerts catch snooping before auditors do.
- Prompt and file inspection before PHI reaches external AI tools
- Role-aware alerting for unusual patient-record access patterns
- Audit-ready incident logs for HIPAA investigations and remediation
Legal Services
Privileged Information
A paralegal pastes a confidential merger document into ChatGPT to summarize it. Now privileged information is in a third-party AI's training data—attorney-client privilege compromised.
Shield intercepts sensitive documents before they leave your network and redacts them automatically. Privilege stays privileged.
- Inline detection of privileged matter names, deal terms, and client identifiers
- Redaction or block workflows before browser-based AI submission
- Custody logs that show what was attempted, flagged, and stopped
Finance
Client Data Protection
A trader uses AI to analyze a client portfolio. The model inadvertently exposes trading strategies and client names in its output—compliance breach and competitive intelligence leak.
Shield scans AI outputs in real-time and masks client data before anyone sees it. FINRA-ready audit trails included.
- Detection for account numbers, portfolio identifiers, and client PII
- Output scanning and masking before sensitive model responses circulate
- Policy enforcement that maps cleanly to compliance review and supervision
Insurance
Claims and Underwriting Control
Claims adjusters and underwriters use public AI to summarize incident narratives, policy documents, and claimant records. That convenience creates leakage risk across regulated personal and financial data.
Shield classifies regulated claims content before submission, enforces redaction rules, and creates a forensic trail for each intervention.
- Detection for claimant identifiers, policy numbers, and payout-sensitive records
- Workflow-safe redaction before summaries are sent to external copilots
- Centralized audit evidence for claims, underwriting, and vendor reviews
Enterprise SaaS
Centralized Governance
Engineering, support, sales, and operations all adopt different AI tools with no central governance. Shadow AI usage creates policy drift, data leakage, and no single enforcement point.
Shield provides centralized browser and AI-session policy enforcement across every AI surface your team touches. One policy plane, enforced everywhere.
- Shared policy controls across browser AI, uploaded files, and prompt traffic
- Real-time block, redact, or alert responses based on data class and destination
- Unified security telemetry for security, legal, and operations leadership
Public Sector
Controlled AI Adoption
Teams are pressured to use AI for speed, but public-sector workflows involve procurement data, constituent records, and controlled operational context that cannot be casually copied into consumer AI.
Shield creates a controlled adoption layer so agencies can permit productivity use without surrendering control over what leaves the environment.
- Pre-submission inspection for controlled records and operational documents
- Allow, redact, flag, or block actions based on agency policy
- Reviewable evidence trail for internal governance and external oversight
Breach Prevention at the Last Mile.
The Shield browser extension is the endpoint sensor that intercepts clipboard data, form submissions, and file uploads in real time — stopping sensitive information before it reaches third-party AI services.
- ✓PII Interception: Automatically detects SSNs, patient records, credit cards, and proprietary data before submission.
- ✓Send-Button Kill Switch: Disables transmission and surfaces a real-time alert when sensitive data is detected in any AI chat interface.
- ✓Compliance Audit Trail: Every interception is logged with timestamps, data categories, and user context for regulatory review.
Simple Trust. Complex Security.
We protect your AI and data using intuitive, battle-tested concepts. Bridging the gap between raw compute and sovereign intelligence.
The Invisible Fence
Airlock acts as an invisible boundary for your AI agents. It ensures your data stays exactly where it belongs, within the yard you control.
The "Invisible Fence" that defines the high-tension boundary between your private context and the public world.
When a violation occurs, the system flags the data for triage instead of blocking it by default, maintaining flow while removing risk.
Ensures your AI only "thinks" and "acts" inside the yard you've authorized, safe from external contamination.
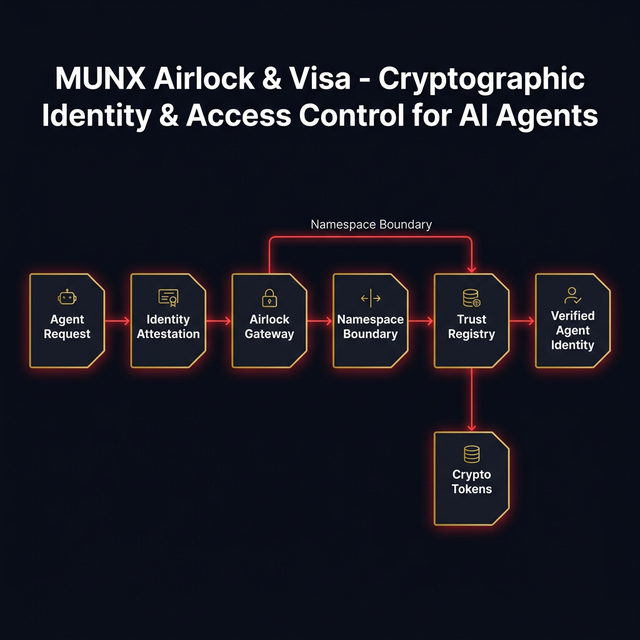
Shared Colors
VISA is the "colors" your agents wear. In a distributed swarm, identity is the only protection against infiltration.
Every action is signed with a cryptographic Sigil. Like a gang's colors, it proves they belong to your realm.
The gateway rejects any agent not wearing your colors. No badge, no data access, no exceptions.
From Visitors to Sovereigns, rank dictates reach. Power is earned, verified, and revocable.
Act I
Multinexus — Your AI Team, Your Hardware
Your agents answer to a SaaS. Shouldn't they answer to you? Multinexus is a self-hosted agentic runtime with 12 specialized AI agents, three-tier persistent memory, and self-correcting protocols. Local-first, no cloud dependency.
12
Agents
3
Memory Tiers
0
Cloud Dependencies
4
Model Support
Fourteen specialized base agents — Architect, Forgemaster, Oracle, Sentinel, and ten more — running on your hardware. No SaaS. No API middlemen. Full sovereignty.
Self-correcting Prophecy protocolConsensus-gated destructive opsMulti-model hot-swap (Claude, Gemini, Codex, Grok)The Blackboard + Prophecy pipeline breaks strategic goals into executable atoms. Planning, execution, and review in a closed loop — no human micromanagement required.
Prophecy strategic planningBlackboard shared workspaceAirlock data isolation protocolHot memory for active context. Warm memory for session history. Cold memory for persistent knowledge. All stored locally — your data never leaves your machine.
Hot: Active context windowWarm: Session graph (Graphiti)Cold: Filesystem checkpointDocumentation
Ready for the technical deep-dive?
The Shield docs cover deployment patterns, classifier benchmarks, and policy configuration — everything you need to evaluate and roll out Shield across your organization.
Open Shield docs